Ransomware attacks continue to haunt businesses of all sizes with losses estimated to exceed $20 billion in 2021. Quantum’s Scalar i3 and i6 tape libraries now offer a system with three escalating levels of protection for data stored on tape. These are Active Vault, Logical Tape Blocking, and Ransom Block, a portfolio of features that can be initiated remotely without human intervention and address data integrity and cyber protection. Of primary focus in this paper, though, is Quantum’s Ransom Block, as it’s the first technology that creates a physical air gap between data tapes and the robotic system inside the library.

To put some context around the importance of ransomware protection, it is estimated that a business was a victim of a ransomware attack about every 10 seconds in 2021. There does not seem to be any let-up projected for 2022. In addition to the financial impact ransomware attacks impose, the impact on a business’s reputation is massive and may not be recoverable. Research has indicated over 65% of attacked organizations suffered significant revenue loss and of those, over 50% suffered reputational damage resulting in job loss. Cybercrime is becoming so pervasive, criminals are employing fake service “help desks” where they can procure methods to stage attacks faster and easier.
So how does the Quantum Scalar Tape system protect enterprise data from potential ransomware attacks? Tape backups are certainly not new and previously there was a downside to using tapes as a backup medium. Traditionally, moving tapes offline meant physically exporting them from an automated tape library and having an operator take them to a container in a secure location. The exercise is error-prone with the potential for tapes getting misfiled, lost, or incurring physical damage in the process, not to mention the cost of using third-party vendors.
It’s safe to assume a ransomware attack will occur, and if successful, could result in huge financial losses along with a hit to the organization’s reputation. The key is to recover quickly with little impact on operations and, hopefully, stay off the evening news.
Quantum has developed a set of features to address the impact of a ransomware attack. Understanding these technologies is critical before walking through the technical application in a live environment. Below is a summary of each, with key benefits and use cases articulated.
Quantum Active Vault
The Active Vault feature can be considered “level 1” in the security hierarchy. Active Vault enables tapes to be moved into a secure, isolated in-library vault partition with no network connectivity that is invisible to any application or network. Providing an additional layer of security on top of tapes stored in an active partition, there is a small risk of data compromise in the event the tape library is hacked. Active Vault works with any application and eliminates the dangers inherent in manually handling tapes or removing them from the library.
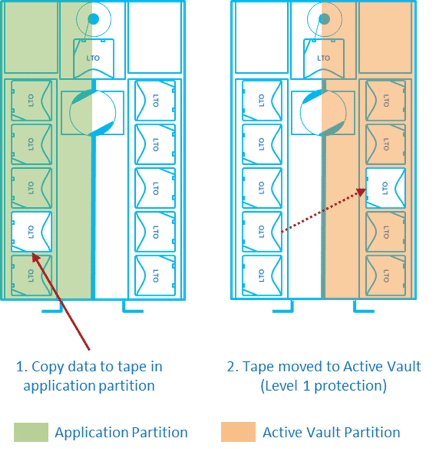
The Active Vault software license provides for an air-gapped copy of data that is also protected from human error. Additionally, it provides for the creation of a totally offline and inaccessible vault within the library itself, creating a secure “ransomware-free” partition. The automated in-library vaulting cuts out the manual complexity of physically handling tapes or transporting them, greatly reducing the chances of tape damage, contamination, or human error.
For protection against “bit rot” and to ensure that vaulted data will be readable and intact when it is needed, tapes in an Active Vault partition can be scanned for media errors proactively if desired, using an optional feature known as Enterprise Data Lifecycle Management (EDLM). Perhaps best of all, Active Vault partitions may use unlicensed slots within the library, further reducing the cost of vaulting tapes. The library operator may use the Scalar remote GUI to remove tapes from the Active Vault partition and return them to the application partition.

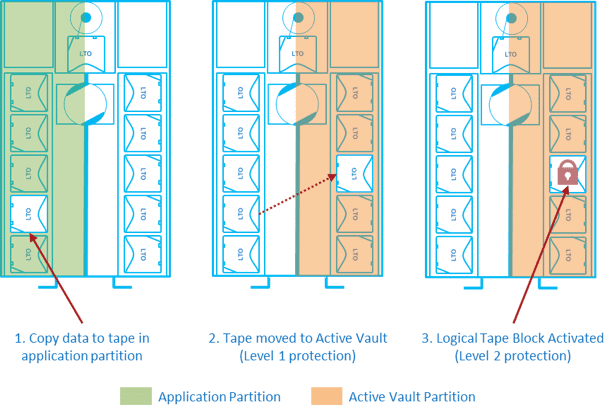
Logical Tape Blocking
Logical Tape Blocking works in concert with Active Vault and represents “level 2” in the security hierarchy. Because tapes may be moved from the Active Vault partition using a remote GUI, there is a small chance that a sophisticated remote attacker could still access them. Logical Tape Blocking prevents this.
Using a software policy-based block placed on a tape magazine, Logical Tape Blocking denies future requests to move tapes out of the Active Vault partition, such as into a drive, providing an additional layer of security on top of Active Vault. To gain access to blocked tapes, the magazine must be ejected from the library and then re-inserted, requiring an operator to be physically located at the tape library. Logical Tape Blocking may be used on its own but is ideally used with Active Vault and Ransom Block to provide the best security.
Ransom Block
All software can have vulnerabilities. No software can be guaranteed as 100% hackproof. Logical Tape Block is implemented in software, so the possibility exists, however unlikely, that a remote attacker could overcome it and gain the ability to attack vaulted tapes. Ransom Block completely eliminates this possibility by creating a physical air gap that no remote attack can overcome.
Ransom Block employs a simple and unique concept to create a physical barrier between data stored on tapes and the network-connected tape library. Tapes stored in the library sit in magazines. When Ransom Block is activated on a magazine, Quantum’s patent-pending design partially ejects the magazine so the tapes cannot be picked by the robot until an operator physically re-inserts the magazine.
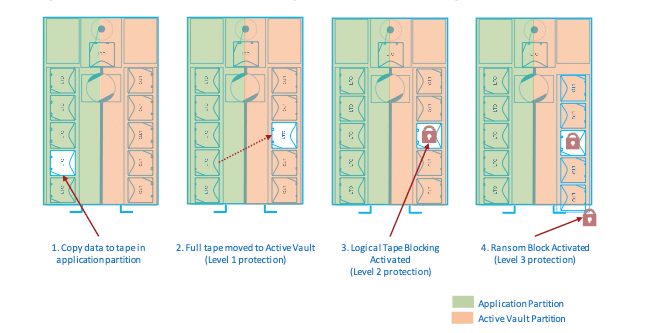
Although partially ejected, the barcode scanner on the robot can still scan the tape barcodes, allowing system administrators to perform periodic audits of the tape system, ensuring tapes are still present.
The tapes are inaccessible until an operator, who must have physical access to the tape library, re-inserts the magazine. Ransom Block provides the highest layer of security. It protects data on tapes from remote attack as securely as exporting the media and putting it in a vault, but with the advantage that their presence may be verified at any time, even remotely.

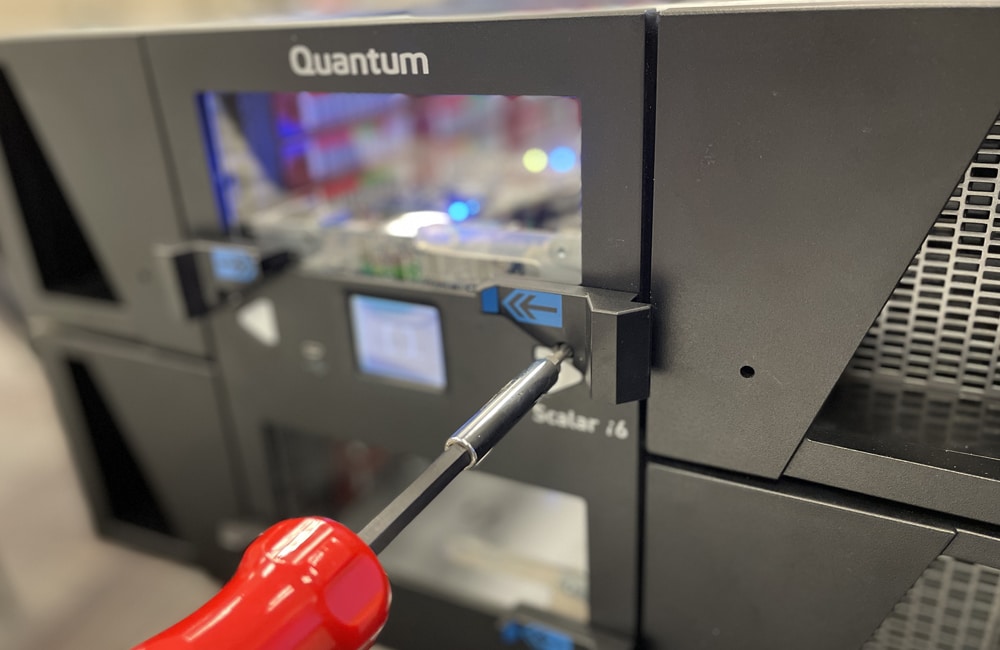
As much as most of Quantum’s data protections are based on software, Ransom Block, while initiated via software, is a hardware solution. Interestingly, Quantum has had this in the plans for some time as Scalar units sold over the last many months have been equipped with the mount points needed to add the Ransom Block hardware after the fact.
The process is very simple for adding the Ransom Block kit if being equipped after the initial purchase. It’s only the bracket and release switch kit that needs to be installed for the magazines. The tape robot is already equipped to be able to actuate the switch to eject the magazines. The Ransom Block stoppers simply limit the magazine ejection distance.
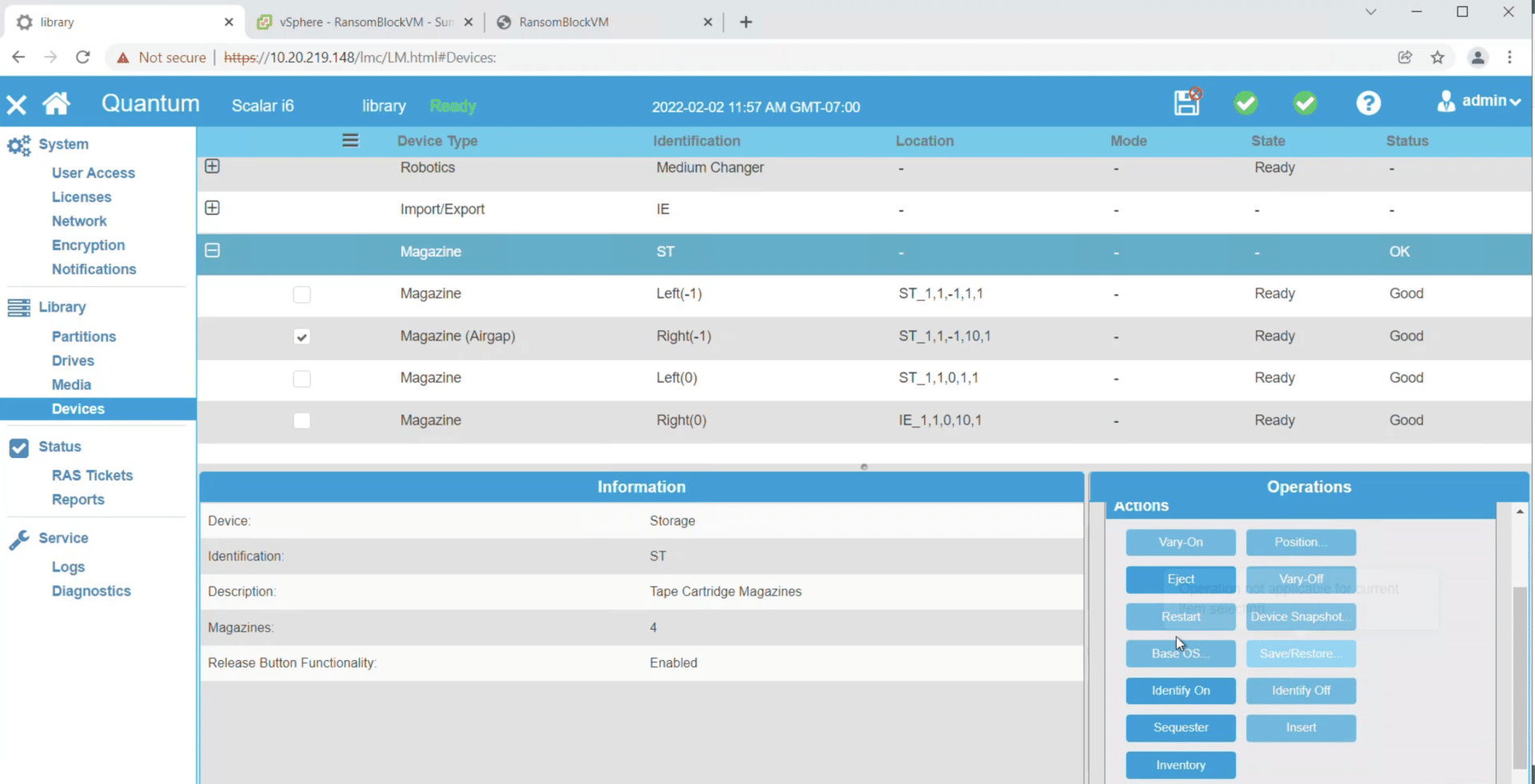
Once the backups are complete, the operator can select one or more magazines to “sequester” using the library GUI. This partially ejects the magazines, activating Ransom Block. The eject can be set to happen automatically when an Active Vault magazine is filled with tapes. To return tapes to circulation, the library operator sends an “import” request for the magazine from the library GUI, then snaps the ejected magazine back into the library. This action also disables Logical Tape Blocking on those tapes. From there, it’s back to the Active Vault script, where the admin can move the desired tapes from the Active Vault partition back into the application partition.
How it Works: Veeam and Quantum Scalar Ransom Block
All of the Quantum tape data protection technologies are impressive on their own, but tape libraries do not live on an island; they regularly interact with applications. For this project, we brought in Veeam, a long-time leader in backup and recovery solutions. Veeam also has a deep partnership with Quantum, making the collaboration a natural fit.
The seamless integration of Veeam and Quantum Scalar illustrates how simple it is to protect data from virtually any destructive attack, but it is also essential in protecting that data from ransomware attacks. Ransomware has become a common weapon for hackers to hold data hostage by extorting monies from corporations. And if the payment is not forthcoming, the loss could be catastrophic to the business.
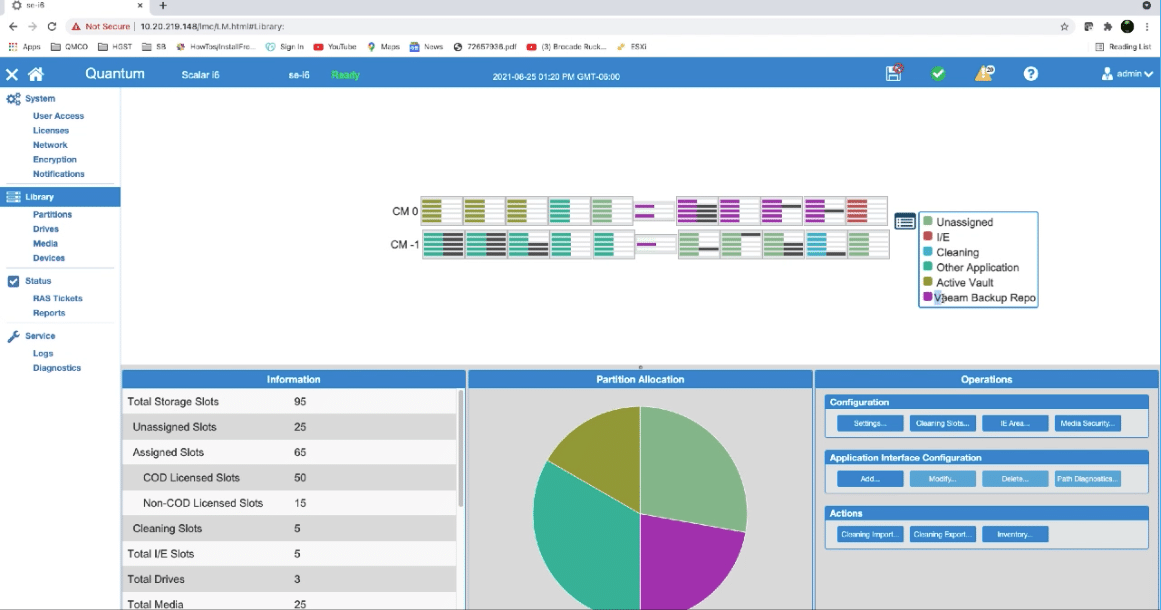
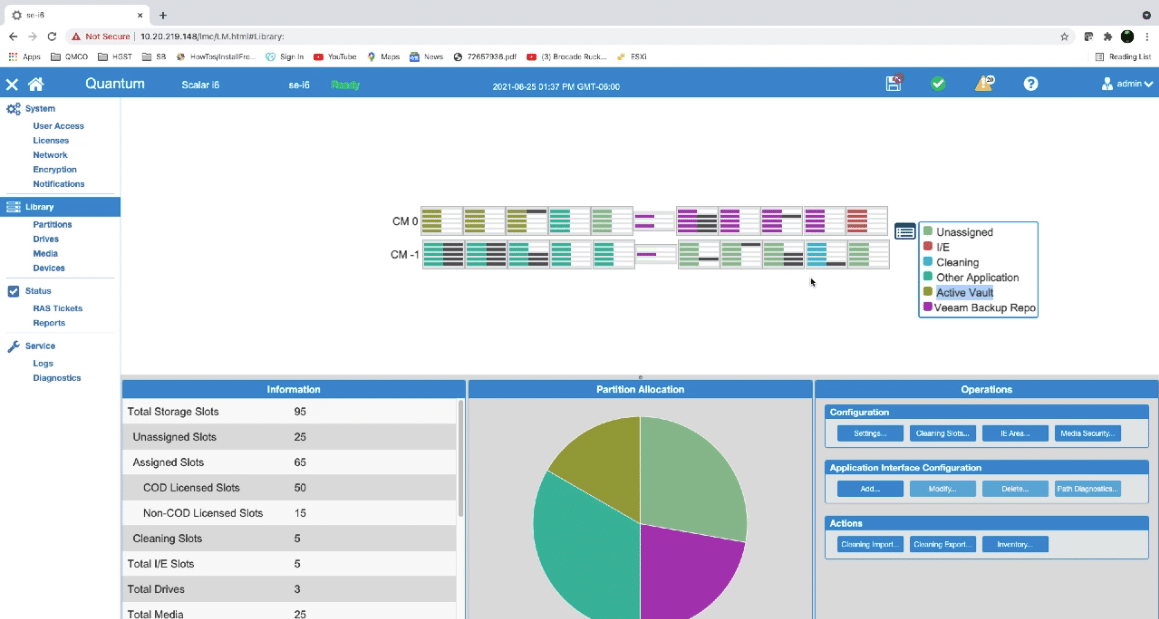
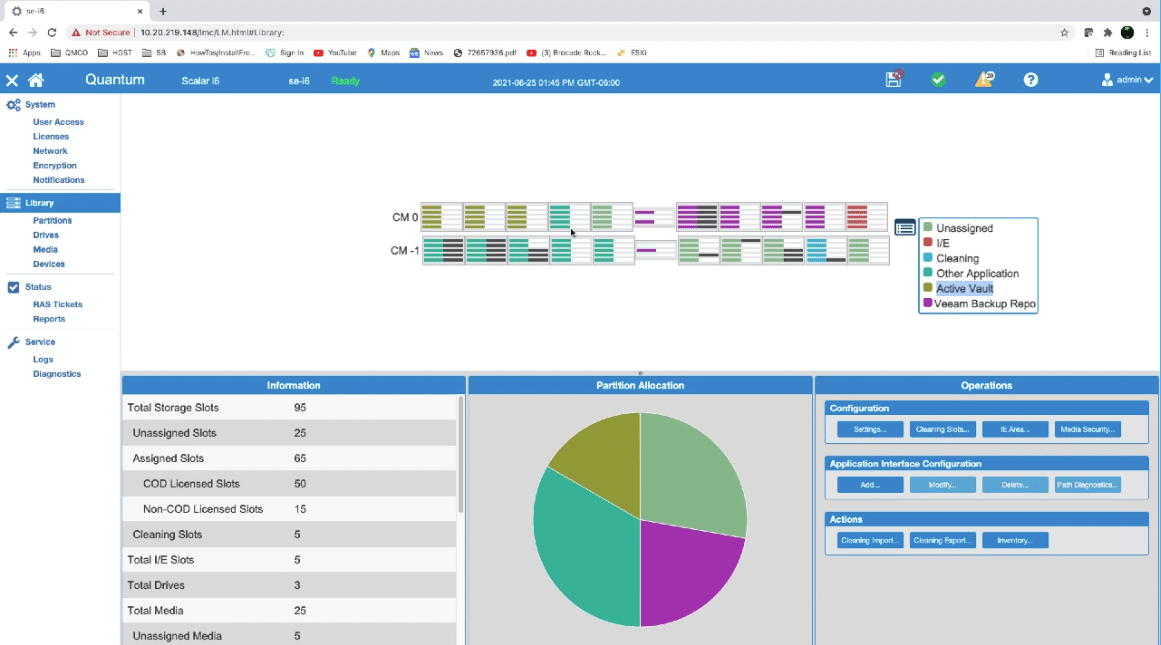
In this demo, two partitions were created in the Scalar Tape Library: one for backup and another for Active Vault. The first thing to look at is the library and what is currently populated in the system. The graphical user interface of the tape library shows what tapes are installed and how they are assigned. Navigating around the system is simple and intuitive.
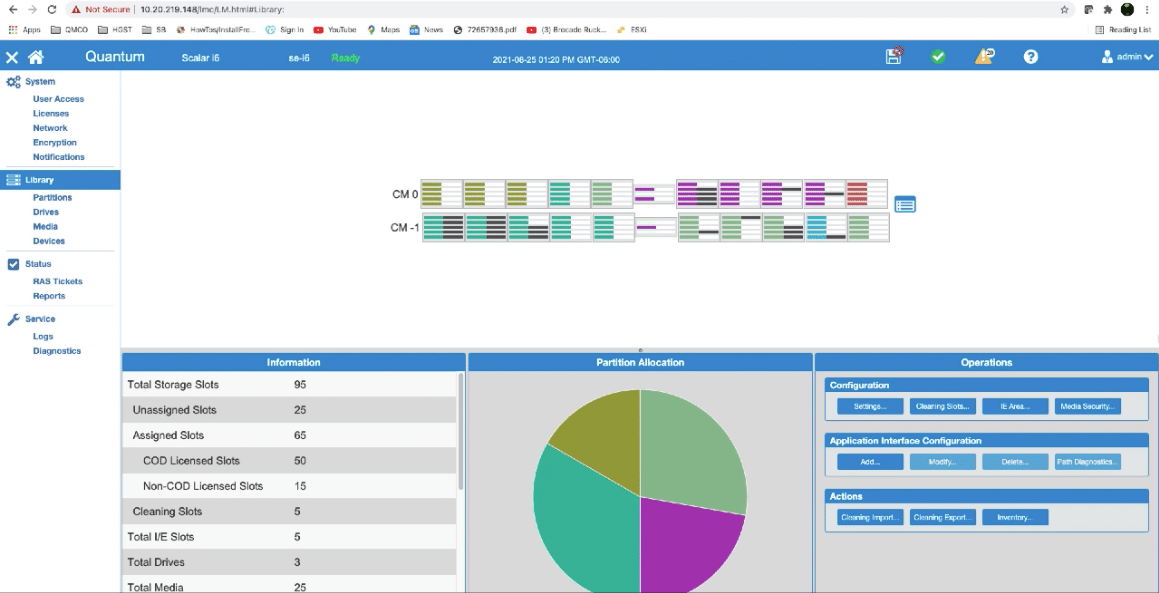
To get a picture of where tapes are assigned and if any tapes are actually installed, the drop-down menu displays where each tape slot is allocated. For this example, Veeam is assigned the purple slots and Active Vault has been assigned the olive slots. A closer look shows that there are six tapes installed in the Veeam library. Those tapes are illustrated by black bars next to the Veeam library slots. Active Vault does not have any tapes installed in that library.
The workflow for this scenario is fairly typical. There is a local repository with a backup partition. There is a tape backup that has been moved to Quantum Active Vault partition. To the system, once the tape has been exported to the Active Vault partition, it is no longer available to the Veeam application.
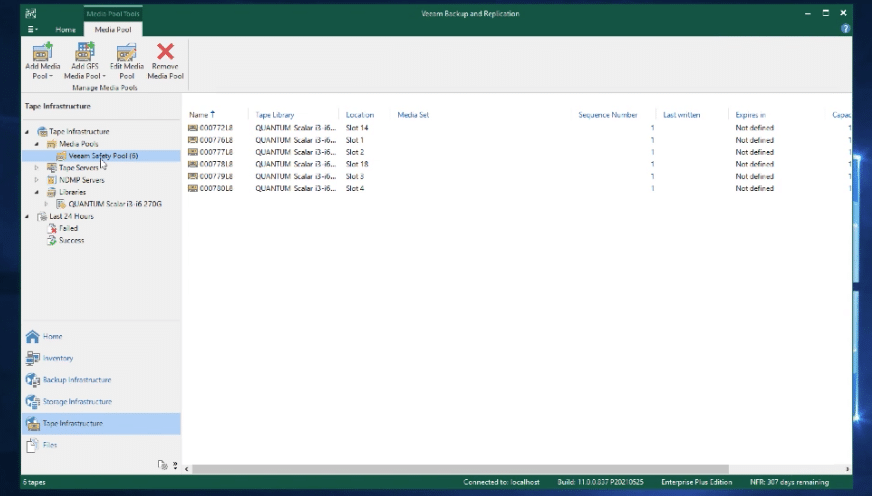
This is what Veeam sees for media in the backup repository. There are six tapes available to the system for Veeam to access. The first thing to do is create a tape job to protect backups. All of these displays are available from the main screen and, for the most part, defaults were used for this demo.
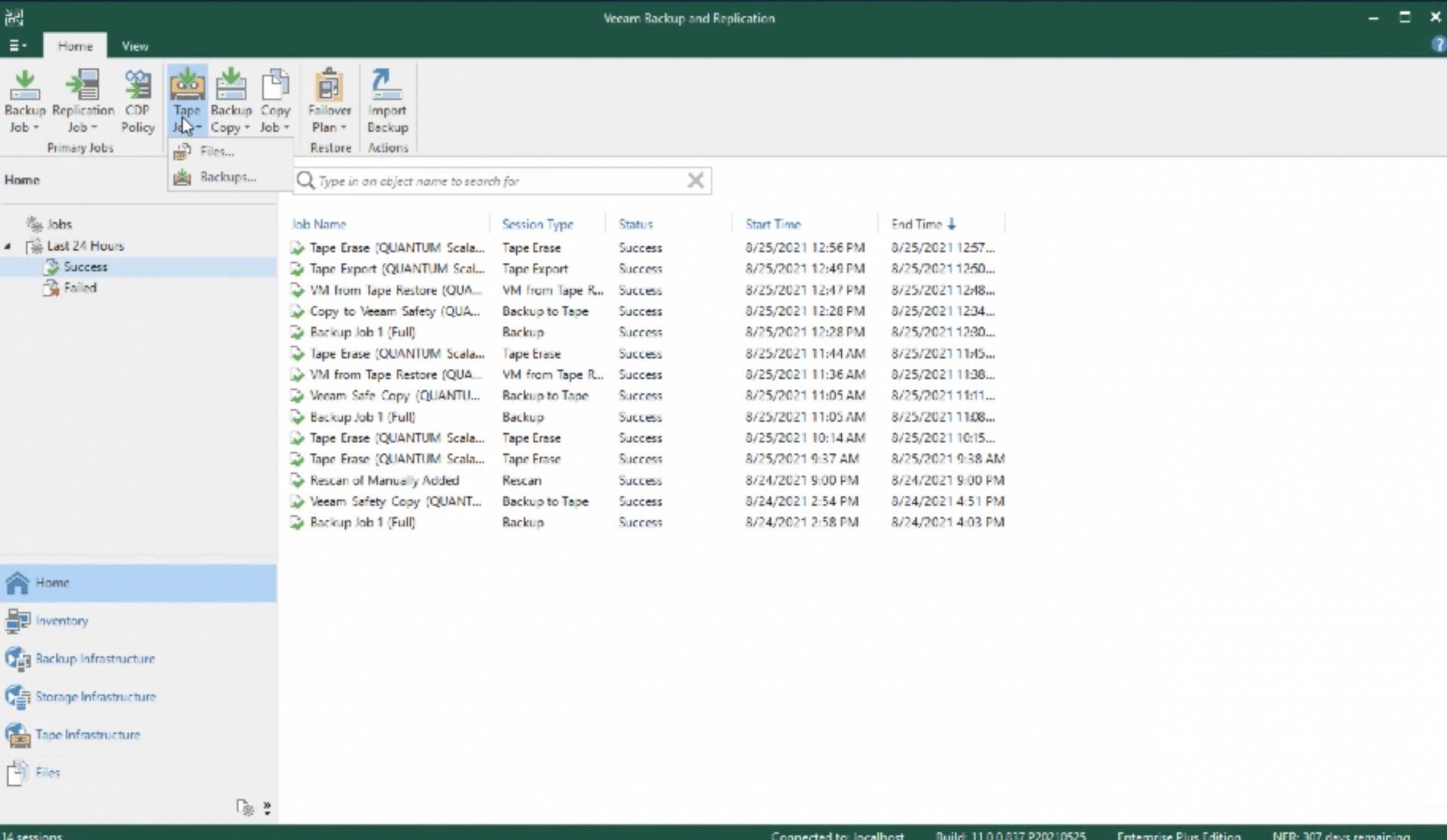
After setting up the backup job, there are options to Eject the media when the job completes or Export the media upon completion. For this exercise, Export was checked.
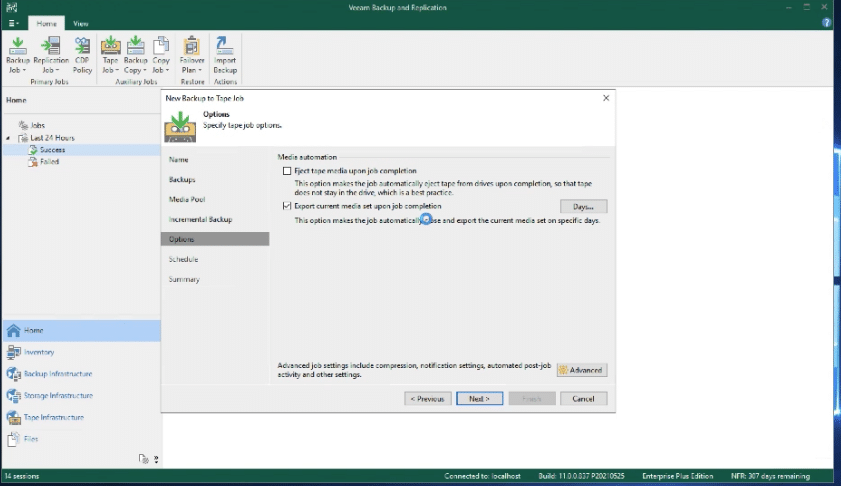
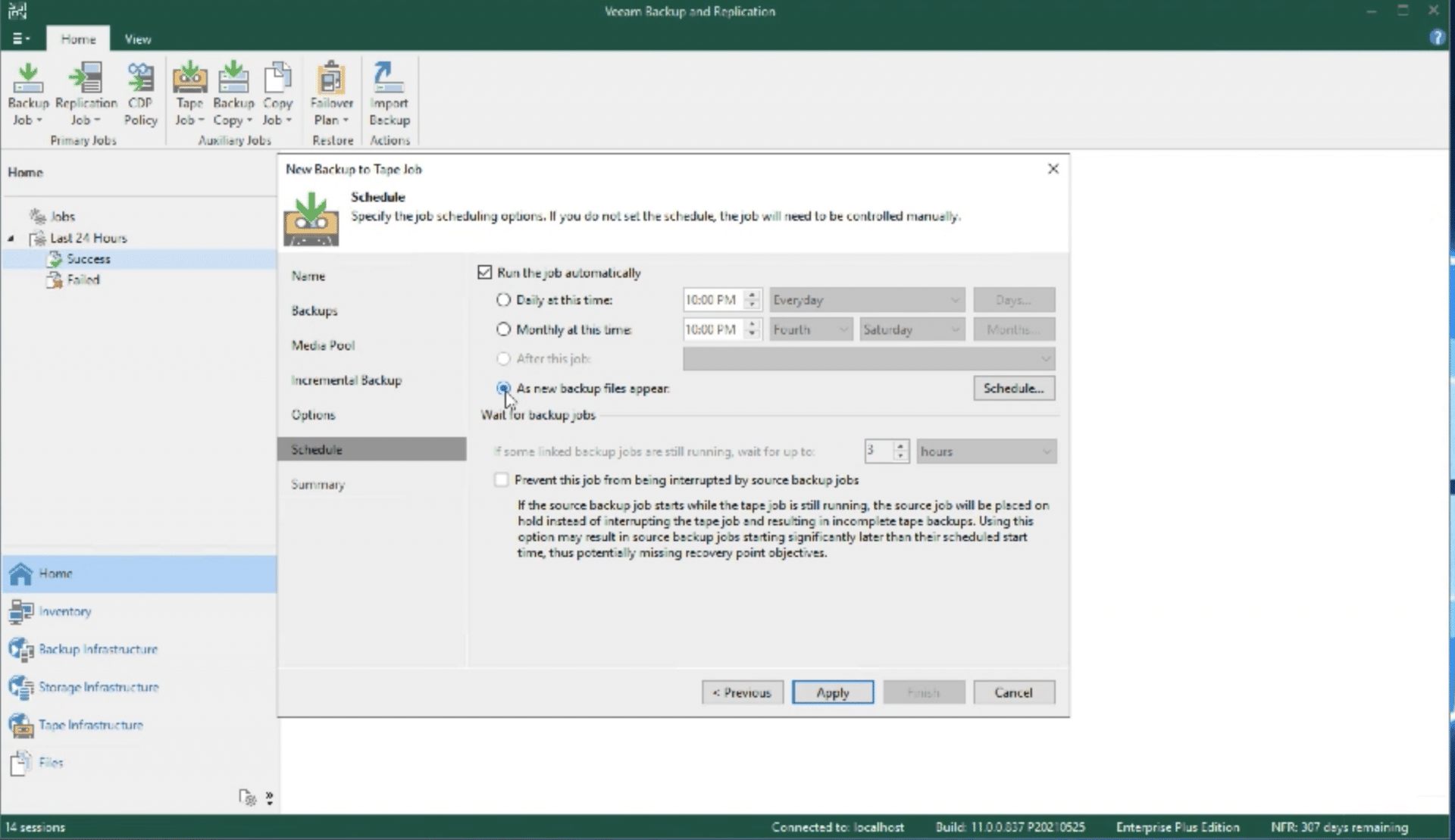
The next step is to schedule the job. Veeam makes the process very simple and by clicking Apply, the new job has been scheduled.
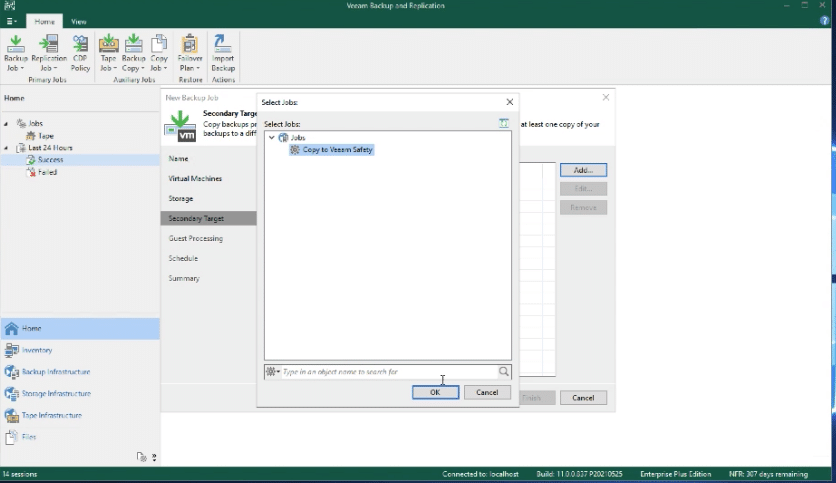
The next step is to create a backup. Again, for this demo, defaults were used and a virtual machine was selected, as well as which repository should be used.
Once the backup job has been created, the job is executed.
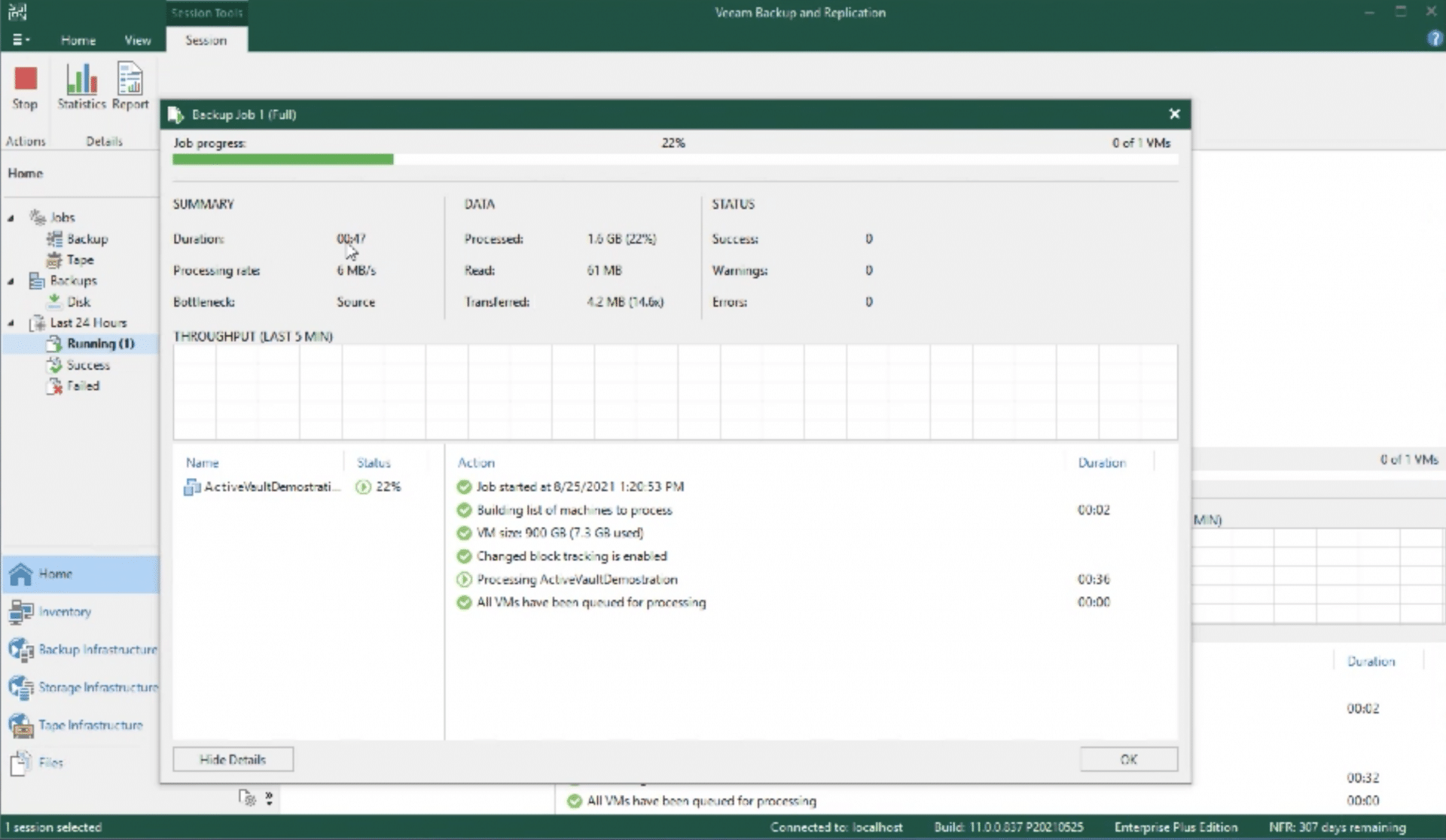
With this particular job, in addition to creating a backup in the backup repository, Veeam was instructed to create a secondary backup media once the backup was completed and the media was exported as shown below.
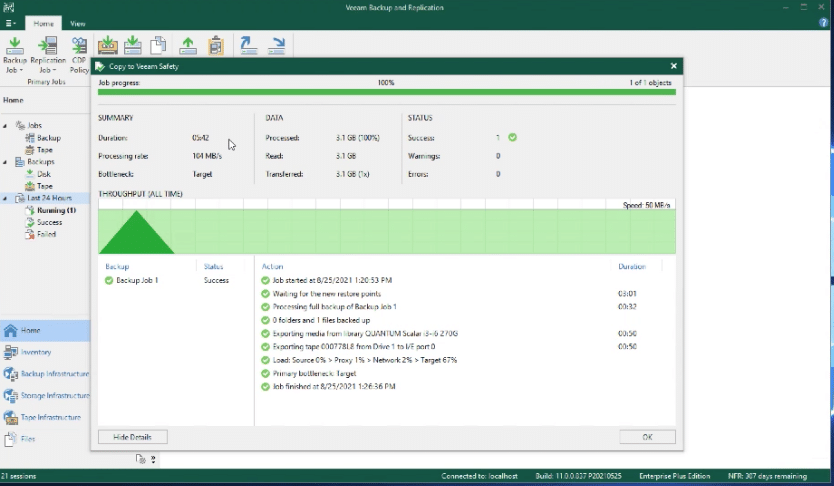
The display now indicates the media has been exported and is considered safe.
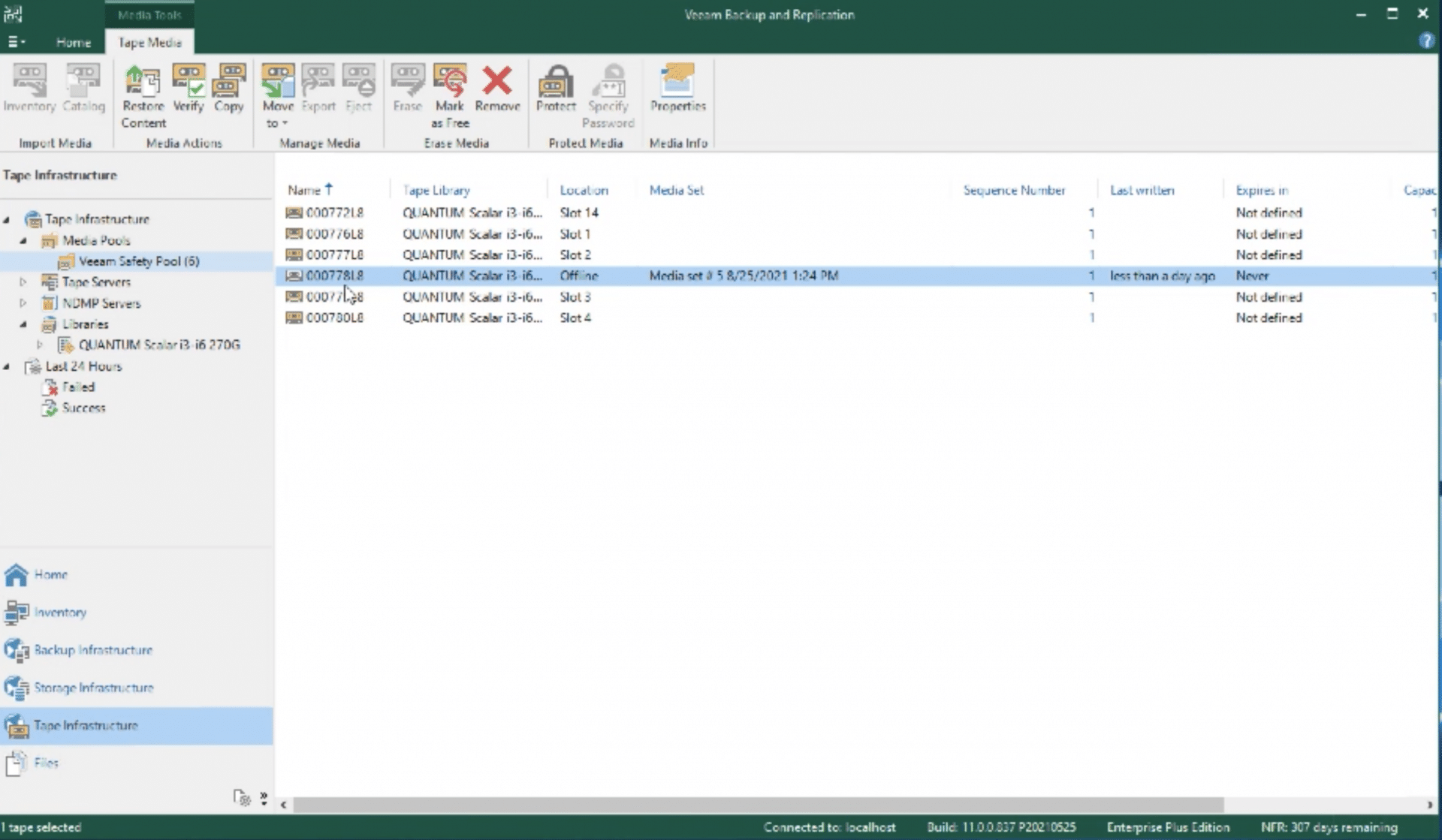
From within the tape library, the Active Vault library now has a tape assigned and one of the original tapes from within the Veeam backup has been moved.
With Logical Tape Blocking enabled, the tape cannot leave the Active Vault partition. From here the administrator uses the library GUI to sequester the tape magazine, ejecting it against the stop, which then activates Ransom Block.
This action secures a safe copy that is inaccessible to the outside world. For the sake of this demo, let’s assume that our Veeam environment was compromised by a ransomware attack. The attacker will go after the backup job to hold it hostage until we pay the ransom. But, we still have our safe copy, so we should be good.
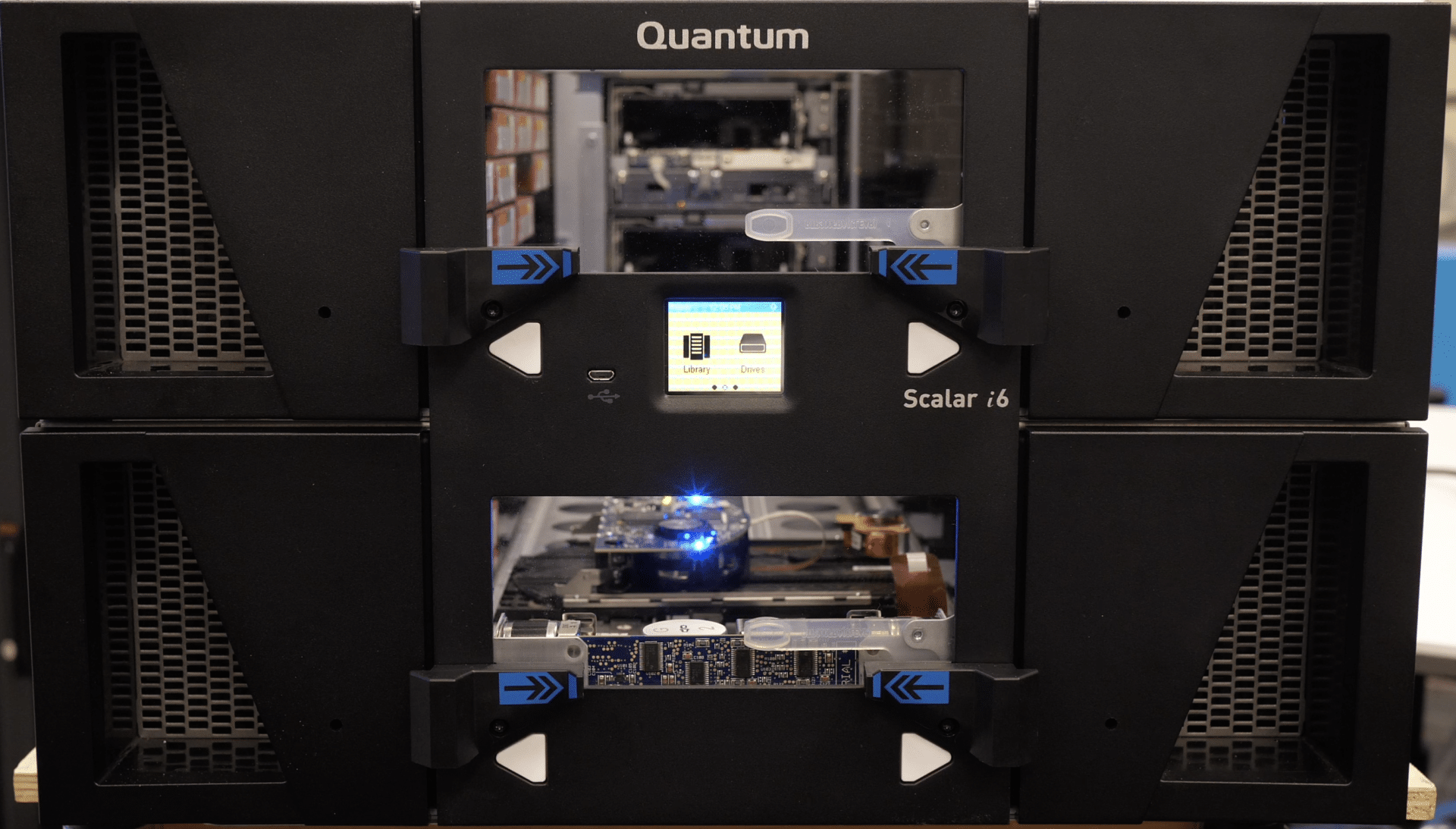
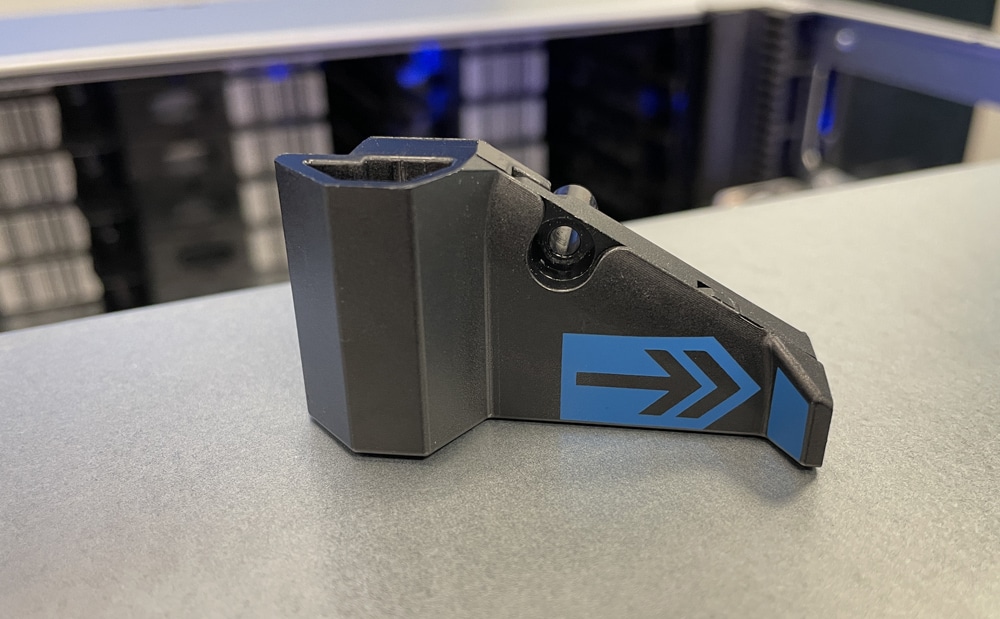
The image above shows the ejected magazine against the stops on the front of the Scalar Tape system.
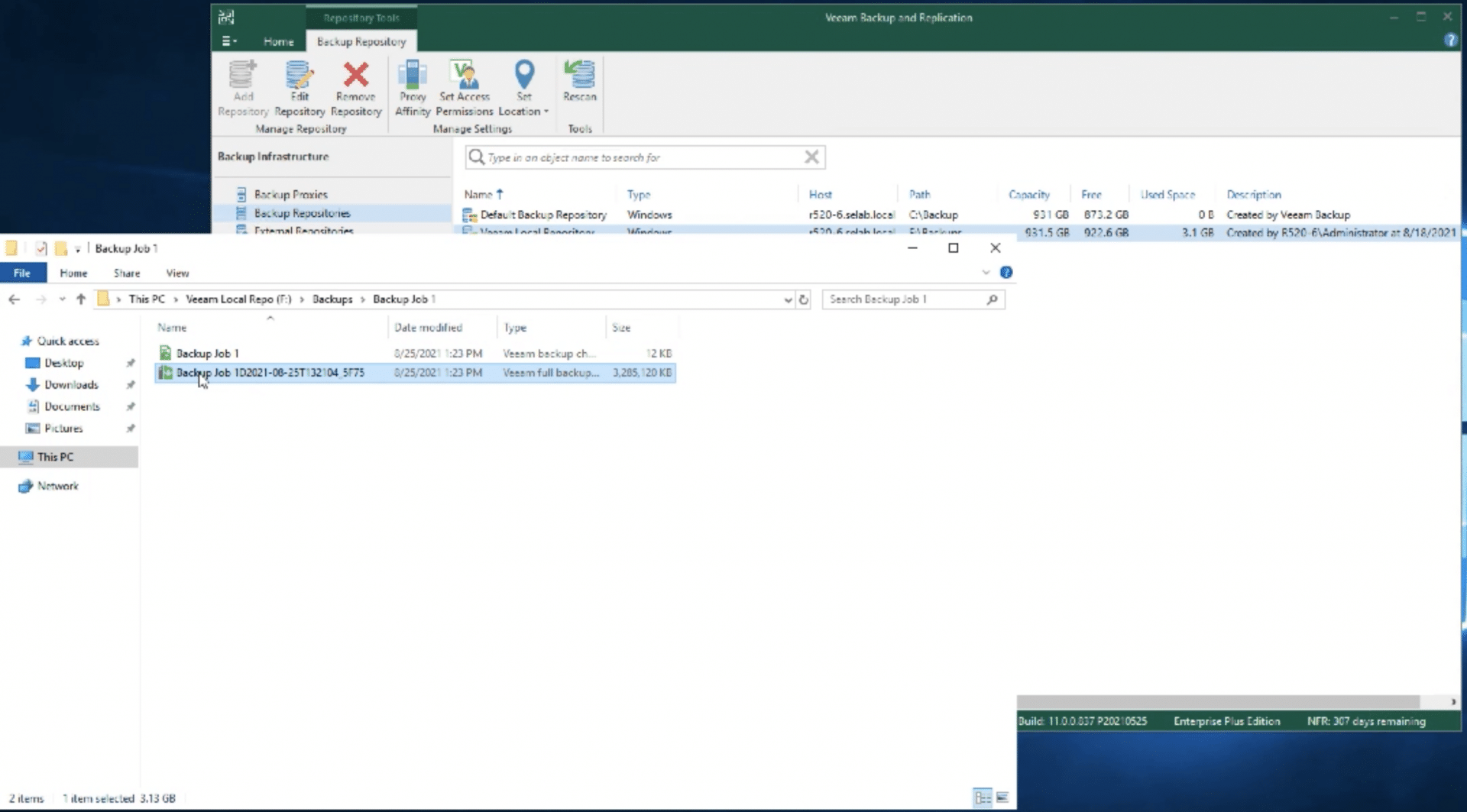
To illustrate the loss of data, the F: drive was erased, and the disk formatted. Now that the data has been erased, it is necessary to restore that drive and get the company back up and operational. It simply takes a call to the tape operator in the data center with instructions to move the tape back to the library and the data can be restored. After manually pushing the magazine back into the library, which deactivates Logical Tape Blocking and Ransom Block, the tape can be moved back into the Veeam partition using the GUI.
From the display above, the tape has been moved from Active Vault back to the Veeam library. At this point, Veeam is instructed to restore backup files from tape to the repository.
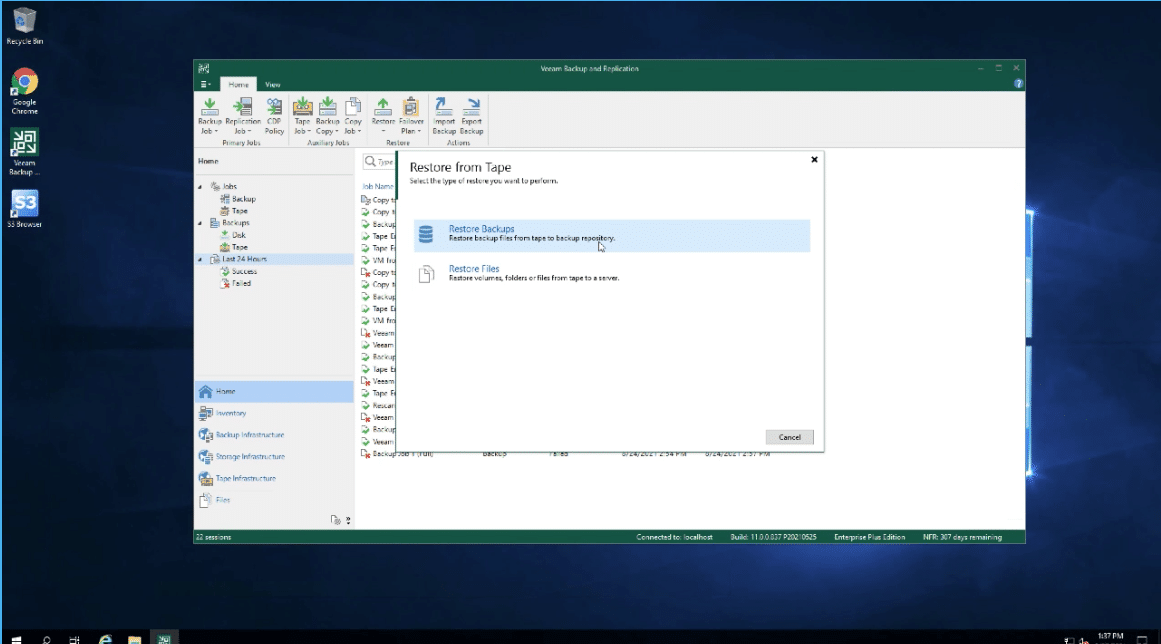
Other than selecting the backup file to restore, that is the entire process for recovering a system following an attack. The tape is exported again to the safety of Active Vault.
There are some key points to focus on from this demo as it relates to Active Vault.
- Ransom Block provides security and protection of vaulted tapes without the need to physically remove the tape
- There is no remote attack path to tapes protected by Active Vault, Logical Tape Blocking, and Ransom Block
- Active Vault is transparent to Veeam
- With just a few steps, an administrator can recover a backup when using these security features
Final Thoughts
Ultimately it takes a comprehensive strategy for an enterprise to be as protected as possible from ransomware attacks. Good data hygiene processes only go so far, and all of the data suggests that if your operation hasn’t been impacted by ransomware yet, it’s just a matter of time. Further, the attacks won’t stop and a modern organization needs to have a plan in place to remediate these issues. While layers of protection are the best bet, there may be a time when even multiple defenses are breached and mission-critical data must be restored. In that event, Quantum Scalar Ransom Block may just be the best last line of on-prem defense you could ask for.

We spent time with both the hardware and the software integrations to get a comprehensive understanding of how Ransom Block works. In a way, it’s an intriguing idea that Quantum engineers leveraged the existing tape robot magazine ejection motion combined with a stopper to create a physical air gap for backup data. On the other hand though, simplicity is often the best way to solve complex problems. For its part, the entire Ransom Block solution is extraordinarily simple to use both on its own and with software partners like Veeam, as we saw in this case.
Ransom Block is available now as a separate license. It is strongly recommended to add this along with the Active Vault license to achieve maximum benefit. As such, adding the hardware bits to any new Scalar purchase is a clear winner. Further, Quantum had this feature on the roadmap for some time, and designed it so that many Scalar units could be retrofitted to add the hardware to support Ransom Block. It’s refreshing to see tape not only alive and well, but also on the leading edge of data protection technologies.
This report is sponsored by Quantum Corporation. All views and opinions expressed in this report are based on our unbiased view of the product(s) under consideration.




 Amazon
Amazon